COMPUTER NETWORKING: A TOP-DOWN APPROACH 8/E (GE)
作(譯)者:KUROSE、ROSS
定價:NT$ 1500
一般會員價:NT$ 1425
一般折扣:95折
供貨狀況:庫存充足
出版日:2021/10/22
出版商:PE
ISBN(13碼):9781292405469
書號:2157608
平裝/800頁/
定 價:NT$1500 元
【內容】
本書特色
- A balanced presentation focuses on the Internet as a specific motivating example of a network and also introduces students to protocols in a more theoretical context.
- UPDATED - Expanded and significantly updated coverage reflects the swift rise in importance of software-defined networking (SDN) and the rapid adoption of 4G/5G networks and the mobile applications they enable arguably the most important and exciting advances in networking in decades.
- UPDATED - Individual chapters have been updated to reflect changes in the field of computer networking:
- Chapter 1 has been updatedto reflect the ever-growing reach and use of the Internet, and of 4G/5Gnetworks.
- Chapter 2, which coversthe application layer, has been significantly updated, including material onthe new HTTP/2 and HTTP/3 protocols for the Web.
- Chapter 3 has been updatedto reflect advances in, and evolution in use of, transport-layer congestioncontrol and error control protocols over the past five years. Updated coverageincludes expanded examinations of TCP CUBIC, the default TCP protocol in manydeployed systems, and delay-based approaches to congestion control, includingthe new BBR protocol, which is deployed in Googles backbone network.Additional coverage studies the QUIC protocol, which is being incorporated intothe HTTP/3 standard.
- Chapter 4, whichcovers the network-layer data plane, has general updates throughout. Anew section is included on so-called middleboxes, which perform network-layerfunctions other than routing and forwarding, such as firewalling and loadbalancing. Timely new material is included on topics such as the amount ofbuffering that is just right in network routers, net neutrality, and thearchitectural principles of the Internet.
- Chapter 5, which coversthe network-layers control plane, contains updated material on SDN, and asignificantly new treatment of network management. The use of SDN has evolvedbeyond management of packet-forwarding tables to include configurationmanagement of network devices as well. Two new protocols are introduced,NETCONF and YANG, whose adoption and use have fueled this new approach towardsnetwork management.
- Chapter 6, which coversthe link layer, has been updated to reflect the continuing evolution oflink-layer technologies such as Ethernet. Also included is an updated andexpanded treatment of datacenter networks, which are at the heart of thetechnology driving much of todays Internet commerce.
- Chapter 7 has beensignificantly updated and revised to reflect the many changes in wirelessnetworking since the 7th edition, from short-range Bluetooth piconets, tomedium-range wireless 802.11 local area networks (WLANs), to wide-area 4G/5Gwireless cellular networks. Coverage of earlier 2G and 3G networks is retiredin favor of a broader and deeper treatment of todays 4G LTE networks andtomorrows 5G networks. Updated coverage of mobility issues, from thelocal issue of handover of mobile devices between base stations to the globalissue of identity management and mobile device roaming among global cellularprovider networks, is provided.
- Chapter 8, which coversnetwork security, has been updated to reflect changes in wireless networksecurity in particular, with new material on WPA3 security in WLANs, and mutualdevice/network authentication and confidentiality in 4G/5G networks.
- Principles and Practice boxes throughout demonstrate real-world applications of the principles studied.
- Case History boxes help tell the story of the history and development of computer networking.
- Material on application programming development is included, along with numerous programming assignments.
- A highly developed art program enhances the descriptions of concepts.
- VideoNotepresentations, programming assignments, Wireshark labs, and additional technicalmaterial are available on the Companion Website at http://www.pearsonglobaleditions.com/.
內容簡介
A top-down,layered approach to computer networking. Unique among computernetworking texts, the 8th Edition, Global Edition, of thepopular Computer Networking: A Top Down Approach buildson the authors' long tradition of teaching this complex subject through alayered approach in a "top-down manner." The text works its way from theapplication layer down toward the physical layer, motivating students byexposing them to important concepts early in their study of networking.Focusing on the Internet and the fundamentally important issues of networking,this text provides an excellent foundation for students in computer science andelectrical engineering, without requiring extensive knowledge of programming ormathematics. The 8th Edition, Global Edition, has been updatedto reflect the most important and exciting recent advances in networking,including the importance of software-defined networking (SDN) and the rapidadoption of 4G/5G networks and the mobile applications they enable.
Chapter 1:Computer Networks and the Internet
1.1 What Is the Internet?
1.1.1 A Nuts-and-Bolts Description
1.1.2 A Services Description
1.1.3 What Is a Protocol?
1.2 The Network Edge
1.2.1 Access Networks
1.2.2 Physical Media
1.3 The Network Core
1.3.1 Packet Switching
1.3.2 Circuit Switching
1.3.3 A Network of Networks
1.4 Delay, Loss, and Throughput in Packet-SwitchedNetworks
1.4.1 Overview of Delay in Packet-Switched Networks
1.4.2 Queuing Delay and Packet Loss
1.4.3 End-to-End Delay
1.4.4 Throughput in Computer Networks
1.5 Protocol Layers and Their ServiceModels
1.5.1 Layered Architecture
1.5.2 Encapsulation
1.6 Networks Under Attack
1.7 History of Computer Networking and theInternet
1.7.1 The Development of Packet Switching: 19611972
1.7.2 Proprietary Networks and Internetworking: 19721980
1.7.3 A Proliferation of Networks: 19801990
1.7.4 The Internet Explosion: The 1990s
1.7.5 The New Millennium
1.8 Summary
Homework Problemsand Questions
WiresharkLab
Chapter 2:Application Layer
2.1 Principles of Network Applications
2.1.1 Network Application Architectures
2.1.2 Processes Communicating
2.1.3 Transport Services Available to Applications
2.1.4 Transport Services Provided by the Internet
2.1.5 Application-Layer Protocols
2.1.6 Network Applications Covered in This Book
2.2 The Web and HTTP
2.2.1 Overview of HTTP
2.2.2 Non-Persistent and Persistent Connections
2.2.3 HTTP Message Format
2.2.4 User-Server Interaction: Cookies
2.2.5 Web Caching
2.2.6 HTTP/2
2.3 Electronic Mail in the Internet
2.3.1 SMTP
2.3.2 Mail Message Formats
2.3.3 Mail Access Protocols
2.4 DNSThe Internets Directory Service
2.4.1 Services Provided by DNS
2.4.2 Overview of How DNS Works
2.4.3 DNS Records and Messages
2.5 Peer-to-Peer Applications
2.5.1 P2P File Distribution
2.6 Video Streaming and Content DistributionNetworks
2.6.1 Internet Video
2.6.2 HTTP Streaming and DASH
2.6.3 Content Distribution Networks
2.6.4 Case Studies: Netflix and YouTube
2.7 Socket Programming: Creating NetworkApplications
2.7.1 Socket Programming with UDP
2.7.2 Socket Programming with TCP
2.8 Summary
Homework Problemsand Questions
SocketProgramming Assignments
Wireshark Labs:HTTP, DNS
Chapter 3:Transport Layer
3.1 Introduction and Transport-LayerServices
3.1.1 Relationship Between Transport and Network Layers
3.1.2 Overview of the Transport Layer in the Internet
3.2 Multiplexing and Demultiplexing
3.3 Connectionless Transport: UDP
3.3.1 UDP Segment Structure
3.3.2 UDP Checksum
3.4 Principles of Reliable Data Transfer
3.4.1 Building a Reliable Data Transfer Protocol
3.4.2 Pipelined Reliable Data Transfer Protocols
3.4.3 Go-Back-N (GBN)
3.4.4 Selective Repeat (SR)
3.5 Connection-Oriented Transport: TCP
3.5.1 The TCP Connection
3.5.2 TCP Segment Structure
3.5.3 Round-Trip Time Estimation and Timeout
3.5.4 Reliable Data Transfer
3.5.5 Flow Control
3.5.6 TCP Connection Management
3.6 Principles of Congestion Control
3.6.1 The Causes and the Costs of Congestion
3.6.2 Approaches to Congestion Control
3.7 TCP Congestion Control
3.7.1 Classic TCP congestion Control
3.7.2 Network-Assisted Explicit Congestion Notification and Delay-basedCongestion Control
3.7.3 Fairness
3.8 Evolution of transport-layerfunctionality
3.9 Summary
Homework Problemsand Questions
ProgrammingAssignments
Wireshark Labs:Exploring TCP, UDP
Chapter 4: TheNetwork Layer: Data Plane
4.1 Overview of Network Layer
4.1.1 Forwarding and Routing: The Network Data and Control Planes
4.1.2 Network Service Models
4.2 Whats Inside a Router?
4.2.1 Input Port Processing and Destination-Based Forwarding
4.2.2 Switching
4.2.3 Output Port Processing
4.2.4 Where Does Queuing Occur?
4.2.5 Packet Scheduling
4.3 The Internet Protocol (IP): IPv4,Addressing, IPv6, and More
4.3.1 IPv4 Datagram Format
4.3.2 IPv4 Addressing
4.3.3 Network Address Translation (NAT)
4.3.4 IPv6
4.4 Generalized Forwarding and SDN
4.4.1 Match
4.4.2 Action
4.4.3 OpenFlow Examples of Match-plus-action in Action
4.5 Middleboxes
4.6 Summary
Homework Problemsand Questions
Wireshark Lab:IP
Chapter 5: TheNetwork Layer: Control Plane
5.1 Introduction
5.2 Routing Algorithms
5.2.1 The Link-State (LS) Routing Algorithm
5.2.2 The Distance-Vector (DV) Routing Algorithm
5.3 Intra-AS Routing in the Internet: OSPF
5.4 Routing Among the ISPs: BGP
5.4.1 The Role of BGP
5.4.2 Advertising BGP Route Information
5.4.3 Determining the Best Routes
5.4.4 IP-Anycast
5.4.5 Routing Policy
5.4.6 Putting the Pieces Together: Obtaining Internet Presence
5.5 The SDN Control Plane
5.5.1 The SDN Control Plane: SDN Controller and SDN Control Applications
5.5.2 OpenFlow Protocol
5.5.3 Data and Control Plane Interaction: An Example
5.5.4 SDN: Past and Future
5.6 ICMP: The Internet Control MessageProtocol
5.7 Network Management, SNMP, andNETCONF/YANG
5.7.1 The Network Management Framework
5.7.2 The Simple Network Management Protocol (SNMP)
5.7.3 NETCONF and YANG
5.8 Summary
Homework Problemsand Questions
SocketProgramming Assignment
ProgrammingAssignment
Wireshark Lab:ICMP
Chapter 6: TheLink Layer and LANs
6.1 Introduction to the Link Layer
6.1.1 The Services Provided by the Link Layer
6.1.2 Where Is the Link Layer Implemented?
6.2 Error-Detection and -CorrectionTechniques
6.2.1 Parity Checks
6.2.2 Checksumming Methods
6.2.3 Cyclic Redundancy Check (CRC)
6.3 Multiple Access Links and Protocols
6.3.1 Channel Partitioning Protocols
6.3.2 Random Access Protocols
6.3.3 Taking-Turns Protocols
6.3.4 DOCSIS: The Link-Layer Protocol for Cable Internet Access
6.4 Switched Local Area Networks
6.4.1 Link-Layer Addressing and ARP
6.4.2 Ethernet
6.4.3 Link-Layer Switches
6.4.4 Virtual Local Area Networks (VLANs)
6.5 Link Virtualization: A Network as a LinkLayer
6.5.1 Multiprotocol Label Switching (MPLS)
6.6 Data Center Networking
6.6.1 Data Center Architectures
6.6.2 Trends in Data Center Networking
6.7 Retrospective: A Day in the Life of a WebPage Request
6.7.1 Getting Started: DHCP, UDP, IP, and Ethernet
6.7.2 Still Getting Started: DNS and ARP
6.7.3 Still Getting Started: Intra-Domain Routing to the DNS Server
6.7.4 Web Client-Server Interaction: TCP and HTTP
6.8 Summary
Homework Problemsand Questions
Wireshark Labs:Ethernet and Home Networking
Chapter 7:Wireless and Mobile Networks
7.1 Introduction
7.2 Wireless Links and Network Characteristics
7.2.1 CDMA
7.3 Wireless LANs
7.3.1 The 802.11 Architecture
7.3.2 The 802.11 MAC Protocol
7.3.3 The IEEE 802.11 Frame
7.3.4 Mobility in the Same IP Subnet
7.3.5 Advanced Features in 802.11
7.3.6 Bluetooth
7.4 Cellular Networks: 4G and 5G
7.4.1 4G LTE Cellular Networks: Architecture and Elements
7.4.2 LTE Protocol Stacks
7.4.3 LTE Radio Access Network
7.4.4 LTE Network Attachment and Power Management
7.4.5 The Global Cellular Network: a Network of Networks
7.4.6 5G Cellular Networks
7.5 Mobility Management: Principles
7.5.1 Device Mobility: a Network-layer Perspective
7.5.2 Home Networks and Roaming on Visited Networks
7.5.3 Direct and Indirect Routing to/from a Mobile Device
7.6 Mobile Management in Practice
7.6.1 Mobility Management in 4G/5G Networks
7.6.2 Mobile IP
7.7 Wireless and Mobility:Impact on Higher-Layer Protocols
7.8 Summary
Homework Problemsand Questions
Wireshark Lab:802.11
Chapter 8:Security in Computer Networks
8.1 What Is Network Security?
8.2 Principles of Cryptography
8.2.1 Symmetric Key Cryptography
8.2.2 Public Key Encryption
8.3 Message Integrity and DigitalSignatures
8.3.1 Cryptographic Hash Functions
8.3.2 Message Authentication Code
8.3.3 Digital Signatures
8.4 End-Point Authentication
8.4.1 Building an Authentication Protocol
8.5 Securing E-Mail
8.5.1 Secure E-Mail
8.5.2 PGP
8.6 Securing TCP Connections: SSL
8.6.1 The Big Picture
8.6.2 A More Complete Picture
8.7 Network-Layer Security: IPsec and VirtualPrivate Networks
8.7.1 IPsec and Virtual Private Networks (VPNs)
8.7.2 The AH and ESP Protocols
8.7.3 Security Associations
8.7.4 The IPsec Datagram
8.7.5 IKE: Key Management in IPsec
8.8 Securing Wireless LANs and 4G/5G Cellular Networks
8.8.1 Authentication and Key Agreement in 802.11 Wireless LANs
8.8.2 Authentication and Key Agreementin 4G/5G Cellular Networks
8.9 Operational Security: Firewalls andIntrusion Detection Systems
8.9.1 Firewalls
8.9.2 Intrusion Detection Systems
8.10 Summary
Homework Problemsand Questions
Wireshark Lab:SSL
IPsec Lab
【關於教科書訂購說明】
☆ 單本即有折扣,將商品放入購物車就可以看見優惠價唷!五本以上團購更便宜!加入會員訂購,還可累積購物金!
★ 若有急需用書,可先LINE私訊詢問庫存呦~
☆ 出貨時間:有現貨的,2個工作日內出貨;無現貨,約3~5個工作日 出貨
【寄送方式說明】
❶ 實體門市取貨
全台麗文校園書局皆可取貨,貨到書局將會以簡訊通知。
❷ 超商取貨
提供7-11及全家超商取貨(需先付款,無貨到付款)。
❸ 一般宅配
本公司主要與黑貓宅急便配合,送達到您指定的地址。
※當您於本網站消費交易完成後,電子發票將會以電子郵件寄給您;如需紙本發票請於下訂時於備註欄位說明。
【付款方式說明】
❶ ATM轉帳、匯款
銀行│第一銀行-三民分行
代號│007
戶名│麗文文化事業股份有限公司
帳號│704-10-051861
※實體ATM每日轉帳最高限額為3萬,若訂購金額超過3萬元,請分兩天或是使用不同的銀行帳戶轉帳。
❷ 信用卡(可分期,需負擔手續費)
凡各家銀行的VISA、MASTER、Union Pay、JCB信用卡皆可使用。

❺ 超商代碼
系統會發送繳費代碼至您的電子信箱,需自行至「超商機器ex:iBon」輸入代碼,產生繳費單後前往櫃檯繳費。
❼ 免卡分期
麗文校園購與「zingala銀角零卡」「第一資融」以及「皮路後支付」合作,讓您免用信用卡就可以購物。
如有使用上的問題,可以先與揪小編聯絡唷!。
※請注意:超過7天未付款之訂單則訂單自動失效;免卡分期訂單成立起7天內未主動聯繫亦同。
【其他說明】
❶關於出貨
1.商品為不缺貨前提下,訂單完成付款後2-4個工作天將會出貨(不含例假日及國定假日);若商品缺貨則須等待1-2週。
2.麗文校園揪來玩保留訂單接受與否權利,若因交易條件有誤或有其他情形導致我們無法接受您的訂單,將以E-mail發送取消訂單通知給您,造成不便敬請見諒。
❷關於退貨
1.非門市現場消費享有七天猶豫期,收到商品當天往後算七天內若是決定不買,則協助不要拆封,一拆封視同願意購買。
2.若真的決定不購買商品要退貨,請聯繫我們LINE線上客服,我們會盡速為您處理。
❸關於新品瑕疵與維修保固
1.全新商品享有購買七日內,新品瑕疵的換新保障;但新品瑕疵與否,是由商品代理商或原廠所判定,麗文校園揪來玩僅能依據判定的結果給予協助。若是原廠判定非新品瑕疵則無法換新,需改為維修的方式處理。
2.新品瑕疵換新的作業時間,將依各廠商的流程而定,最快2個工作天,慢的話也可能需要到15個工作天。
3.購買超過七日後,維修服務由原廠提供。如有需要維修,麗文校園揪來玩可以代為送修,但送修如需運費時(EX:原廠沒有提供免費收件服務),則需由您負擔送修的運費(運費約為100元起,因商品大小而異)。
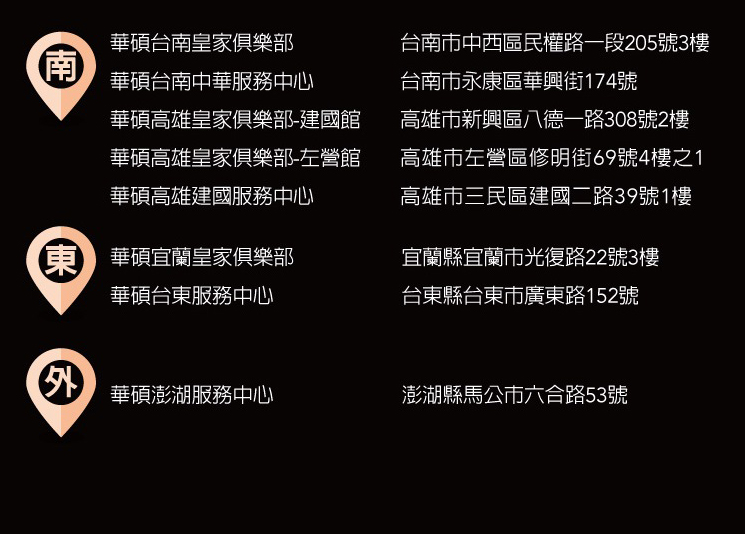
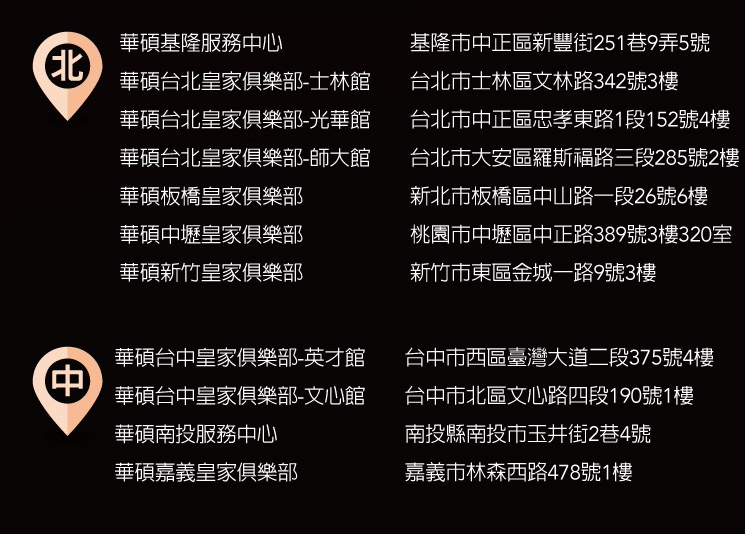
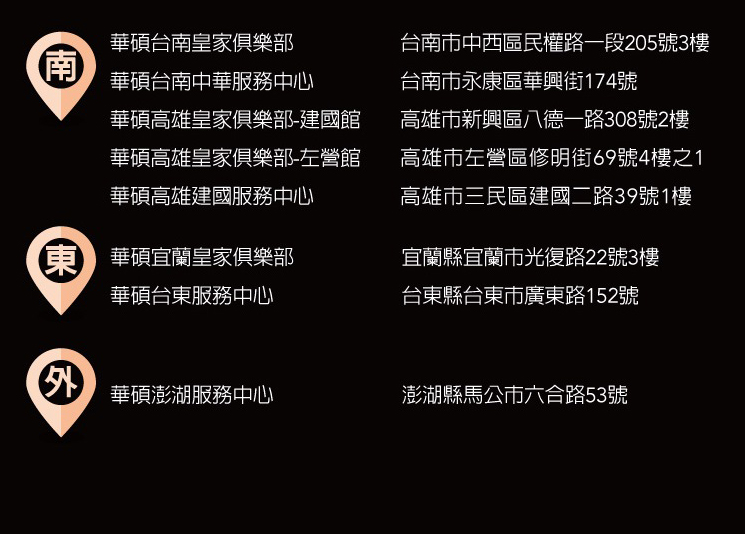
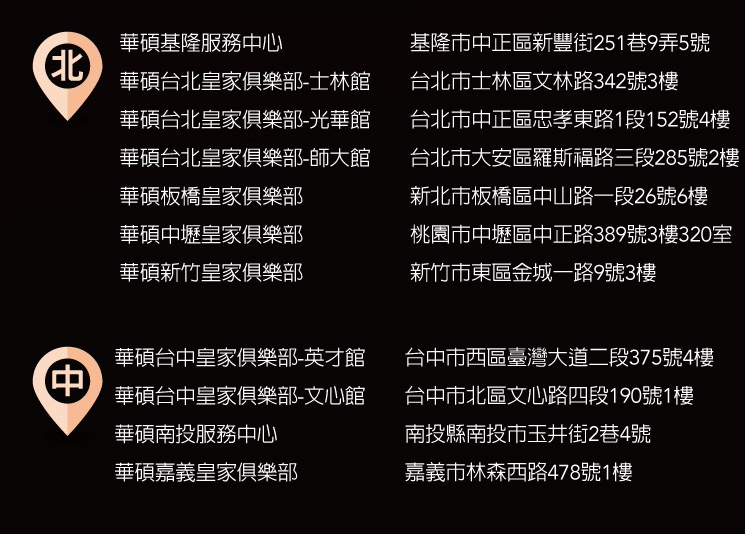
【華碩的維修服務】